A Robust Intrusion Detection Mechanism in Wireless Sensor Networks Against Well-Armed Attackers | International Journal of Intelligent Systems and Applications in Engineering
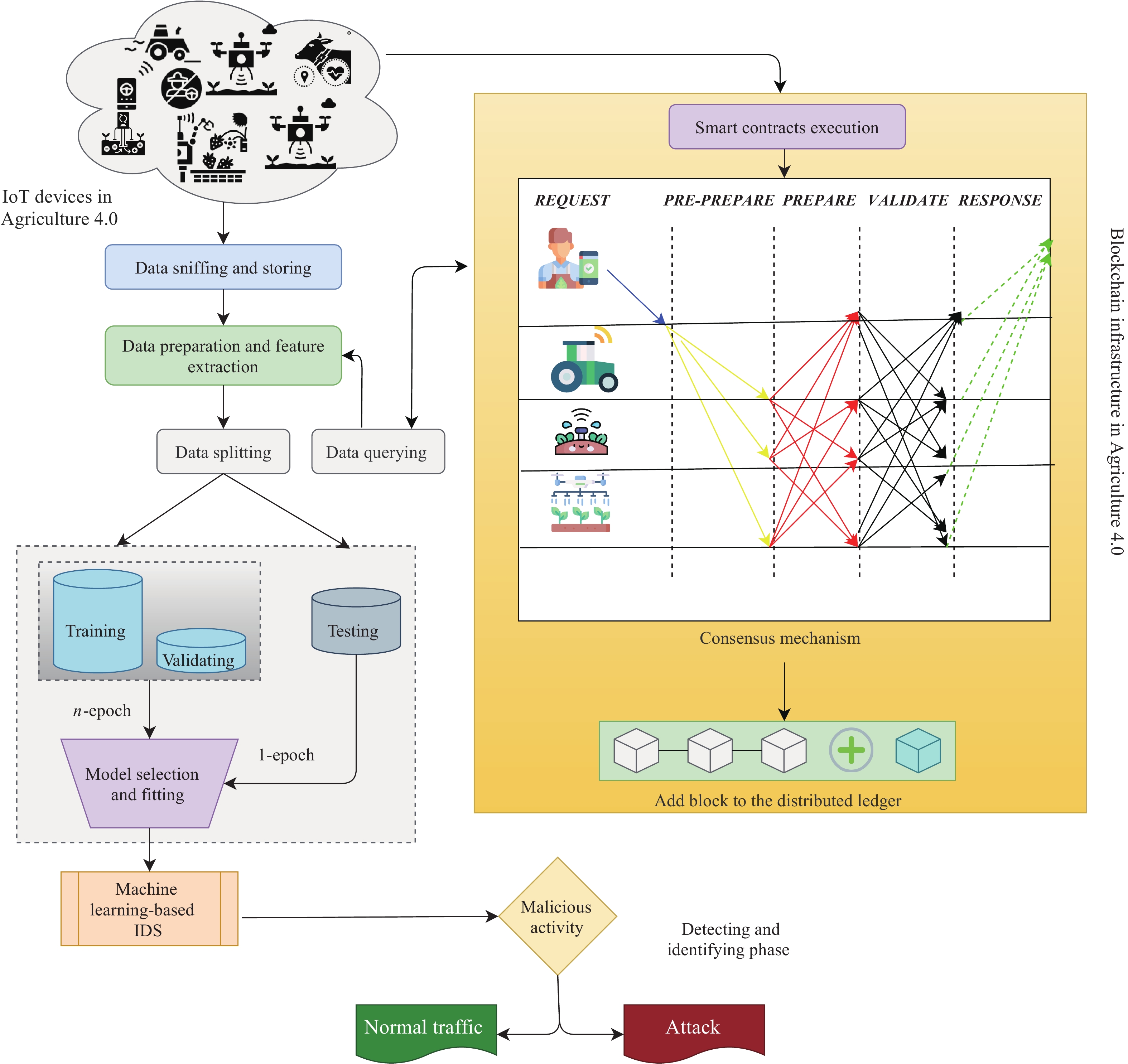
Cyber Security Intrusion Detection for Agriculture 4.0: Machine Learning-Based Solutions, Datasets, and Future Directions
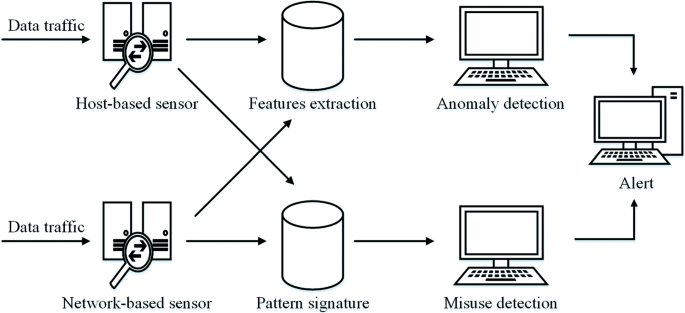
Intrusion detection systems for IoT-based smart environments: a survey | Journal of Cloud Computing | Full Text
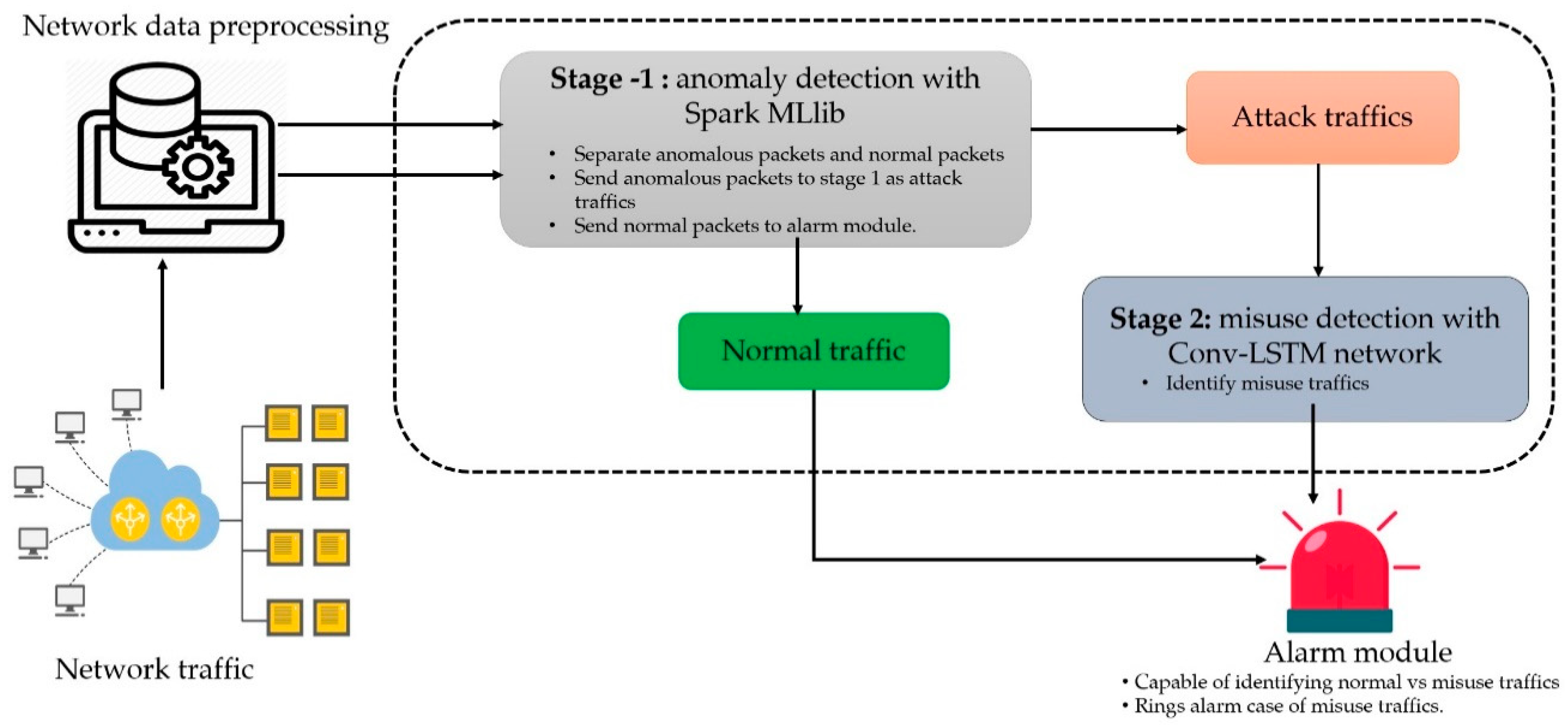
Symmetry | Free Full-Text | A Scalable and Hybrid Intrusion Detection System Based on the Convolutional-LSTM Network

Intrusion Detection with Artificial Neural Networks: Anomaly based Intrusion Detection using Backpropagation Neural Networks: Hossain, Moazzam: 9783639210385: Amazon.com: Books

Network intrusion detection system: A systematic study of machine learning and deep learning approaches - Ahmad - 2021 - Transactions on Emerging Telecommunications Technologies - Wiley Online Library
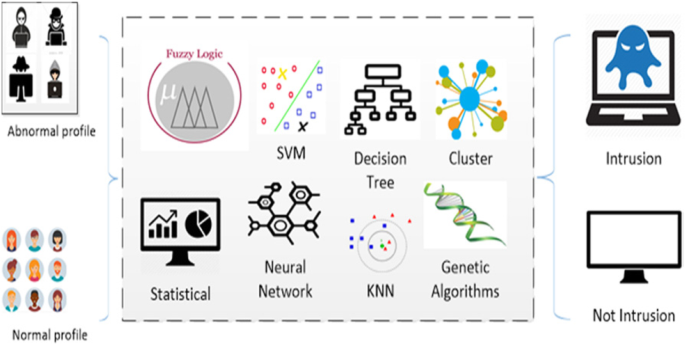
Survey of intrusion detection systems: techniques, datasets and challenges | Cybersecurity | Full Text
Sensors | Free Full-Text | A Hybrid Intrusion Detection Model Using EGA-PSO and Improved Random Forest Method